I’m getting a bit sick of large corporations a) demanding excess data as a condition of doing business with me, b) allowing it to be stolen, and c) giving zero fucks about it.
What are some things that us netizens can do to make our displeasure known.
Extra points for funny ideas.
Edit: whoops, I missed the “il” part in “not illegal”. Anyway you should definitely not do the following. Allegedly doing the following would be arson, and society frowns upon such things.
Easy:
- Identify company
- Wait until it’s a weekend night. We’re not after the wage slaves after all.
- Mix polystyrene and gasoline. Remember that gasoline can melt some plastics, so if using a plastic container for mixing do a test first. You do not want napalm all over the place.
- Fill the gooey substance in glass bottles.
- Cap the bottles. (see #7)
- Drive to the company.
- Open bottles and put wicks in them. (important not to do this earlier. Driving with open gasoline containers in your car will make you drowsy and is a fire hazard)
- If you haven’t already got gloves on, put them on and wipe down the bottles - you may have to leave some at some point.
- Have accomplices trigger fire alarms all over the local fire department’s district. Either automatic fire alarms will be discarded for a bit or the marshall will be tied up investigating.
- Light a wick, throw the bottle at the company, try to get it to break a window.
- If you’re out of bottles or you see blue lights cheese it. Otherwise go back a step and repeat it.
If a company is publicly traded, then all leaked individuals are given 50.1% controlling stock in the company, split among the victims with new stocks created for them, with unclaimed stocks held in a trust controlled by anyone that did respond to claim stocks. They can sell the stocks, or drive the company into the ground out of spite. Maybe even both.
Companies not publicly traded have 3 months to make all code used, trademarked material, and patents open source in perpetuity, and 1 year to convert their corporate structure into a non-profit.
Regardless of the size of the company, the CEO, CTO, and board must eat their weight in fried bugs. They get to pick the type of bug from a list of 5 options, and any seasoning they want. Live streams of the bug eating will be monetized and the proceeds given to orphans, under the title of “It’s not a bug, its a feature.”
Don’t use their services.
The fake name generator might be useful. There are also temporary email services for when a site account requires a confirmed email.
Not exactly what you’re looking for, but Ad-Nauseum is a nice way to inject a ton of garbage into the data corps collect.
Make your data useless or wrong.
More passively, there’s probably an oddly large amount of John Does born on January 1, 2000 ;)
More offensively, anti-image-gen data poisoning such as Nightshade exists. It’s well-defended against IIRC so hopefully someone can Cunningham’s Law correct me. And this is also more solo of a movement (as opposed to gaining mass support for something)
Use EICAR test strings as your password.
If they store your password in plain text the AV will lock the user database.
If your password gets leaked and they are using bad password security, when your password is cracked the AV will isolate the file.
Whoa, I wanna try this now! Thx!
Bold of you to assume a corporation storing passwords in plain text would be using AV
According to EICAR’s specification the antivirus detects the test file only if it starts with the 68-byte test string and is not more than 128 bytes long. As a result, antiviruses are not expected to raise an alarm on some other document containing the test string.
This won’t work, assuming the database file is more than 128 bytes long
I think the important distinction would be ‘file’ or ‘record’. Passwords aren’t really a file in a database iirc and records in a database have a storage limit
deleted by creator
Ah… “advice” consisting of “I’ve heard of a thing”
This is diabolical. I approve.
If you send back one of those reply mail envelopes it costs them money. Stuff those envelopes with junk and send them back.
I don’t get many of them anymore, but when I do, I mail them back with a little slip of paper inside that says “poop”.
But not a brick. They are apparently onto that.
I tried the brick once long ago. 1) No way to verif it works (not just PO’s the P.O. 2) That kind of shit may be why so many public POBoxes have been removed. 3) The was of paper (up to 3.5 oz?) -seems- to have worked.
First class letter mail is up to 3.5 oz and within a certain l thickness. Every ounce costs extra over the first oz (idk about commercial return mail pricing) just stuff it with flat cardboard from cereal boxes or fill out the information wrong and put in a competitors corporate address.
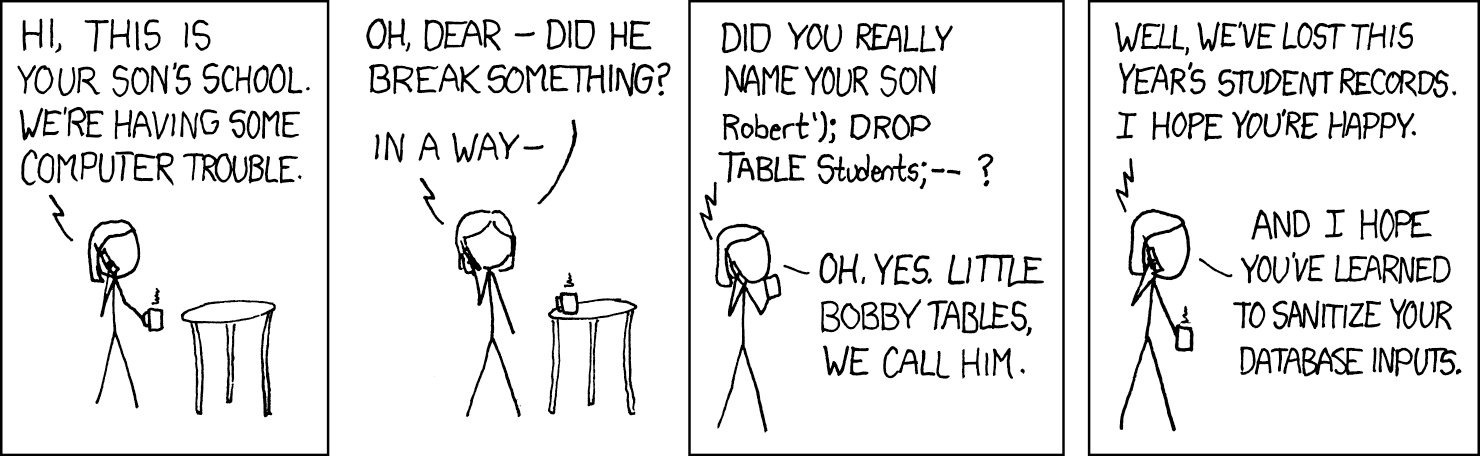
Explanation for illiterates?
https://www.explainxkcd.com/wiki/index.php/327:_Exploits_of_a_Mom
SQL sanitization joke. Won’t affect most databases today.
Still, any programmer worth their salt should filter their inputs. One group at work refuses to do it and they always get away with it and it’s infuriating
As others have said, the best instances of direct action are illegal.
- Get into politics
- Get elected
- Rip them a new one
*might take some time
More in the spirit of this, prefer and actively seek out alternatives that collect as little or even no data at all and test to make sure they run without internet access. If they give you a hard time or straight up dont work without an internet connection when they ought to be able to, chuck em
Edit: also call them out in reviews. Why you collect data guys, dont you want my money?
that only works when there are alternatives that work offline. which is not guaranteed.
This has been the go-to for decades and it’s not working. I feel like we need to be prepared to engage with the system, but make it clear we are not just passive consumers. Something that becomes viral maybe?..
Pick a C*O. Set fire to them.
Alternatively, if you want to go to the source, pick the single investor (dereferencing through any institutional investor) with the greatest worth, and set fire to them.
In the case of managed investors, flip a coin to decide if you burninate an investor or someone with purchasing authority.
I believe this is illegal in most jurisdictions.
We’ll see once the verdict comes
The only right answer.
Use AI to generate false info to feed into their database
I love putting wrong AI slop in every optional field or space I can get away with for profiles and accounts that don’t really matter.
If an extension exists for this I’ll use it
I’m skeptical that anything legal will work for very long because they will quickly work to make said legal action illegal.
But we can have some fun along the way, and it does change behaviour for a bit.